What It Does
Monk controls who can do what across your organization. You define roles with fine-grained permissions, assign them to team members, and every action gets logged. That’s it. No policy files, no YAML, no third-party auth layer.RBAC
You create custom roles. Each role gets explicit permissions over specific resources. Permissions are actions matched against resource patterns. Enforcement happens server-side, so it doesn’t matter whether someone’s using the extension or hitting the backend directly. Resource types:- Templates, Secrets, Images (environment-scoped)
- Builds, Clusters, Workspaces
- Org members, Org roles, Org settings
- Audit (team or self scope)
read,write,admin,*deploy(templates),use(secrets)
/templates/**— all templates/environments/staging/secrets/**— secrets in staging only/clusters/**— all clusters/audit/team/**— team-wide audit events
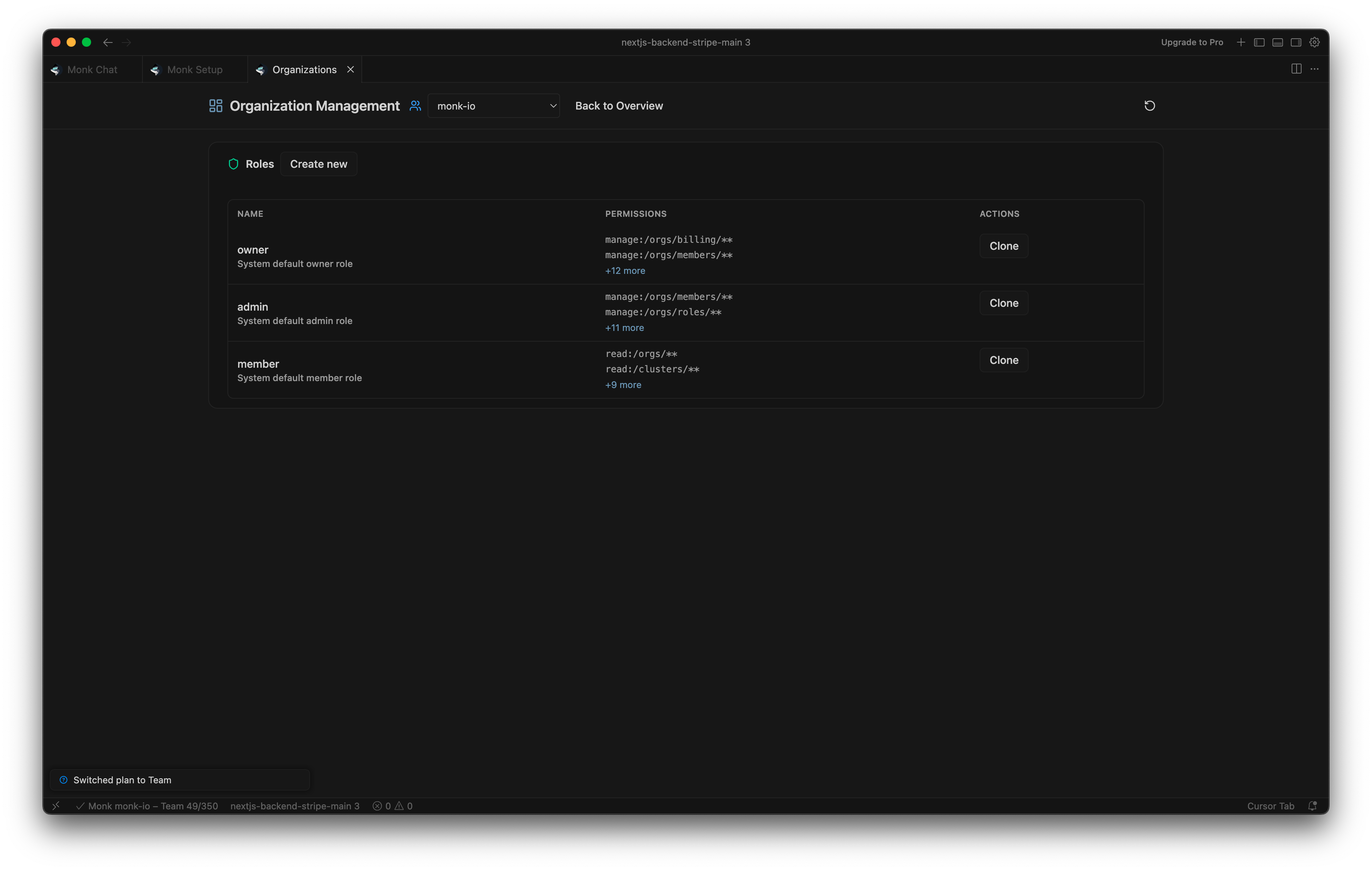
Managing RBAC in the UI
Open the Organization panel and click Manage Roles. Creating roles:- Click Create new
- Enter role name and description
- Add permissions — select resource type, action, and optional environment
- Click Create Role
Managing RBAC via Chat
You can do all of this through chat too.Audit Logging
Every action in your organization gets recorded. Builds, deployments, cluster operations, secret changes — all of it, with actor, status, and trace info attached. How to view:- Welcome screen: Recent events show up in the Team Events card.
- Activity panel: Open it from the Monk Dashboard for the full timeline.
Not Available Yet
Single sign-on, domain enforcement, and org-wide 2FA aren’t available yet.Team Collaboration
Organizations, members, and shared clusters
Multiple Environments
Environment-scoped permissions and isolation